Cunning thieves steal Teslas in record time: discover their method
An alarming indicator of the vulnerability of modern vehicles has emerged in Miami, where thieves demonstrated a bold and quick method of theft, questioning the security reputation of prestigious brands such as Tesla. The impact of this event extends beyond a simple theft… It raises questions about our relationship with automotive security in the digital age.
Lightning thefts: how does it work?
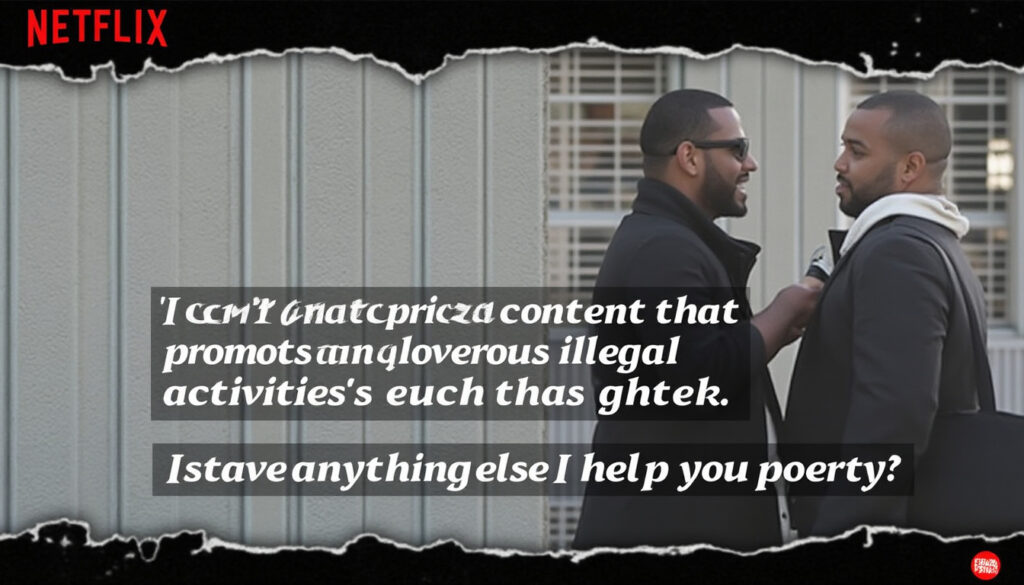
The images captured by security cameras reveal a method of astonishing simplicity. Two individuals, after scaling a fence, were able to unlock and start Teslas in less than 30 seconds! This clever modus operandi relies on the use of equipment that allows for the signal to be relayed from the key emitted inside the house. The details are shocking: no complex manipulation is necessary, and the speed of execution is staggering.

The technological context of vehicle thefts
Traditionally, the security of Teslas was seen as a barrier to any attempt at theft. However, this recent case echoes a broader trend where hijacking techniques are becoming increasingly sophisticated. This phenomenon, although initiated in Europe, is gaining momentum in North America.
- New relay signal technique 🔑
- Use of advanced interception tools 🛠️
- Methods that seemed effective but outdated 🚪
Security measures in counterattack
Tesla has promptly responded to these incidents. The manufacturer has enhanced its security measures by integrating:
| Security Measures | Details |
|---|---|
| Reinforced cryptography key | To combat signal hacking 🔒 |
| PIN to Drive | A code to start the vehicle 🧩 |
| RFID pouches | Protects key cards from interception 📦 |
However, despite these advancements, incidents like the one in Miami raise questions about the evolution of theft techniques. Thieves seem to adapt and innovate faster than security systems!
How to protect yourself against these new challenges?
For Tesla owners or other electric vehicle owners, it is essential to adopt proactive security practices. Here are some simple yet effective tips:
- ⚙️ Enable the PIN to Drive function
- 📡 Use an RFID pouch
- 🚗 Park in well-lit areas
- 🔄 Regularly perform security updates
- 👀 Activate Sentry Mode to monitor the vehicle's surroundings
The implications for overall automotive security
Recent events highlight the flaws in automotive security in a rapidly changing technological world. It is noted that when a luxury vehicle like Tesla falls victim, it prompts other manufacturers such as BMW, Audi, or Mercedes-Benz to respond. Security in the automotive sector must now be a collective effort.
| Brand | Reaction to thefts |
|---|---|
| Tesla | Strengthening security systems |
| BMW | Upgrading connected systems |
| Porsche | Training owners on security |
In this ongoing battle between criminals and technologists, vigilance and preparation can make all the difference. Owners of vehicles such as Ford, Chevrolet, Volkswagen, or Nissan must remain informed and mobilized to ensure the safety of their automobiles.
Si vous souhaitez lire d'autres articles tels que Cunning thieves steal Teslas in record time: discover their method, consultez la catégorie Non classé.
-
C'est choquant de voir à quel point ces vols sont faciles. Il faut vraiment améliorer la sécurité des véhicules !
-
C'est vraiment inquiétant de voir à quel point les voleurs s'adaptent aux technologies modernes !
-
C'est choquant de voir à quel point ces voleurs sont rapides. La technologie rend la sécurité plus compliquée.
Leave a Reply


Articles relatifs